Introduction
The adventure unfolds as I press forward in my exploration of ethical hacking and penetration testing. In the dynamic landscape of my “Breakout Lab,” I persistently delve into the intricacies of exploiting vulnerabilities, aiming to enhance my skills and showcase hands-on expertise to potential recruiters. Join me on this ongoing journey as I navigate through the challenges posed by the next set of vulnerable boxes in my lab setup.
Network Architecture and IP Assignment
Utilizing VirtualBox, I meticulously crafted a network architecture where each vulnerable box operates in “host-only” mode which sets the IP in this range 192.168.56.XXX, isolating them from external networks. Simultaneously, the Kali Linux attack box, acting as the gateway, is bridged to the internet and set to “host-only.” The meticulous IP assignment, exemplified in the first lab with an IP of 10.192.56.101, ensures a controlled testing environment.

Reconnaissance: Nmap and Enum4Linux

The initial phase involved a comprehensive Nmap scan to identify open ports and running services. Building on this, I employed enum4linux to enumerate information, uncovering local usernames “cyber” and “nobody.” This early reconnaissance laid the groundwork for subsequent exploitation.

Web Interface and Hidden Messages
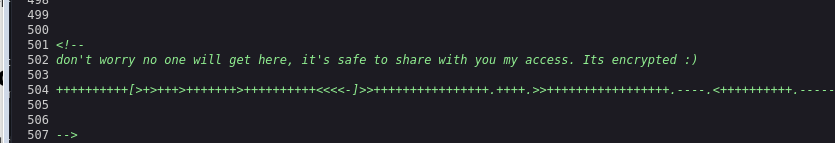
Upon navigating to the web interface at http://192.168.56.101, my scrutiny led to the discovery of a concealed message in the source code. Decoding this message, initially believed to be “Hello, World!” using ChatGPT, revealed its encoding in Brainfuck. However, cross-referencing with dcode.fr yielded a distinct result (“.2uqPEfj3D<P'a-3“), hinting at potential relevance for future exploits.

Port Scanning and Webmin Exploitation

Facing a roadblock with SSH due to a closed port 22, I conducted an exhaustive all-port scan. This revealed an open port 200000 running “MiniServ 1.981 (Webmin httpd).” Leveraging the discovered credentials from the decrypted Brainfuck message, I successfully gained access, securing a reverse shell and the coveted user flag.


Privilege Escalation: Unmasking Capabilities
Observing the presence of a tar program, I initiated “./tar” to glean information. Encountering limited results, I employed the command “getcap -r / 2>/dev/null” for a comprehensive capability analysis. This recursive listing of file capabilities in the root directory, with error messages redirected to /dev/null, became the linchpin for a successful privilege escalation strategy.

Root Access: Decrypting Hidden Passwords
The culmination involved uncovering a password within a system folder. Employing the “./tar” operation to reveal the contents of “.old_pass.bak,” I extracted the root password. Armed with this key, I ascended to root access, marking the triumphant conclusion of the sophisticated exploit in the Breakout Lab.


Conclusion
As I forge ahead in my ethical hacking journey, the Breakout Lab remains a dynamic arena for hands-on experimentation and skill refinement. The challenges faced, lessons learned, and victories celebrated contribute not only to personal growth but also to the development of a robust skill set for potential recruiters to witness. Stay tuned for more updates as I navigate the uncharted territories of ethical hacking and share insights from the evolving chapters of my cybersecurity odyssey.
