
Introduction: In my ongoing commitment to advancing my skills in cybersecurity, I’ve embarked on an exciting journey that involves the powerful trio of Kali Linux, Docker, and WebSploit. This blog post aims to provide a glimpse into my experiences and objectives as I explore the realm of ethical hacking within the WebSploit Labs environment, curated by the esteemed cybersecurity expert, Omar Santos.
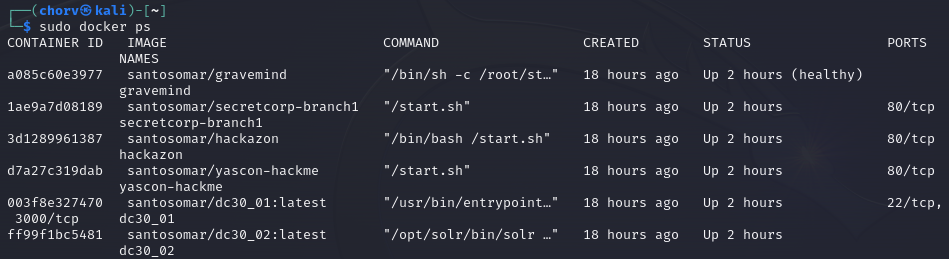
Setting the Stage for Ethical Hacking: Creating a tailored and secure environment is crucial for meaningful ethical hacking endeavors. I’ve meticulously set up my Kali Linux environment with Docker, ensuring a controlled space for exploration. My focus is on utilizing WebSploit tools to crack intentionally vulnerable machines within the WebSploit Labs, demonstrating my dedication to hands-on learning and skill enhancement.
What is WebSploit: WebSploit Labs, a brainchild of Omar Santos, serves as a dynamic learning environment for cybersecurity enthusiasts, ethical hackers, and those passionate about digital forensics. Featuring intentionally vulnerable applications within Docker containers, the platform operates on Kali Linux or Parrot Security OS. With over 9,000 cybersecurity resources, WebSploit Labs offers an immersive and practical approach to continuous learning.
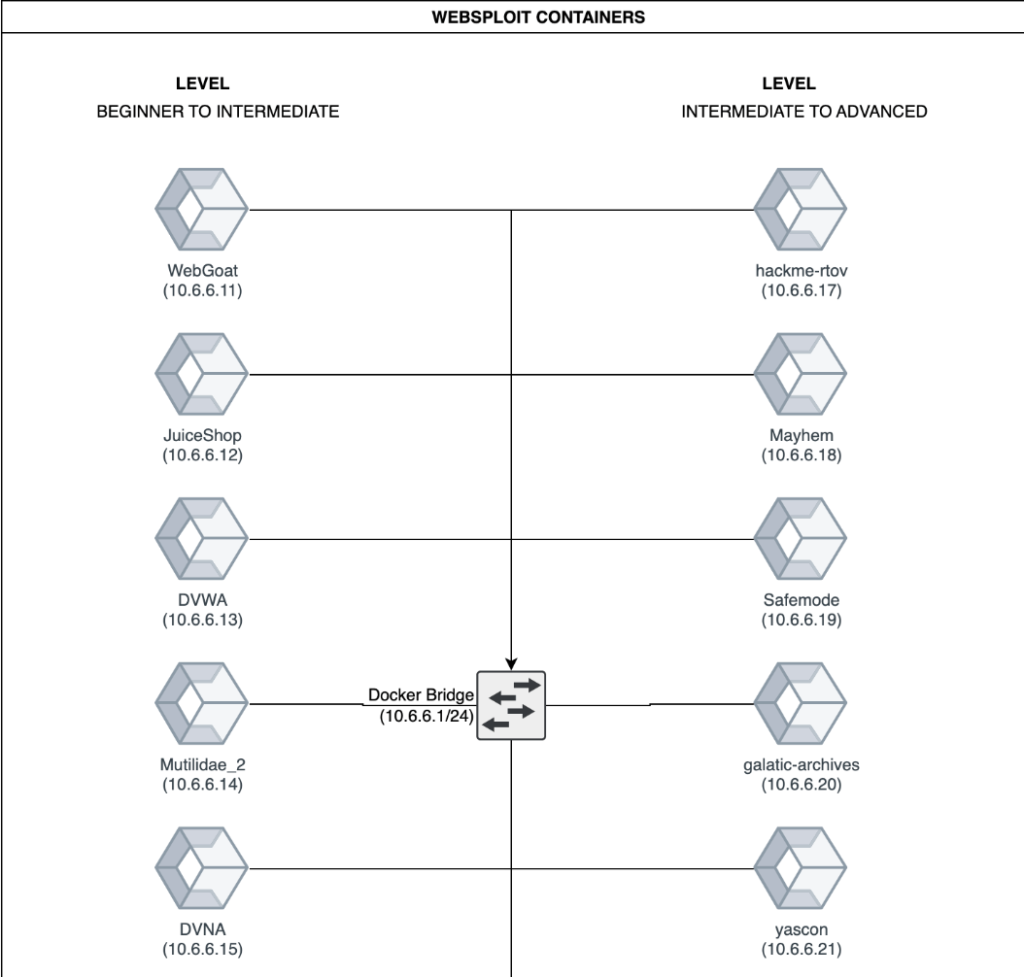
Unveiling WebSploit: Opting for WebSploit was a natural choice for me. The platform provides a seamless way to deploy multiple vulnerable machines directly into my Kali Linux environment. While I’ve tackled individual vulnerable machines previously, the curated challenges within WebSploit Labs and the opportunity to learn from Omar Santos himself have driven my decision to explore this enriching environment.
Tools within WebSploit: WebSploit unfolds a rich array of tools and modules tailored for various facets of ethical hacking. From information gathering to vulnerability scanning and exploitation, each tool serves a strategic purpose in the cybersecurity toolkit. As I immerse myself in this environment, my goal is to not only master these tools but to showcase a comprehensive understanding of their functionalities, reflecting my commitment to continuous improvement.
Future Goals: My engagement with WebSploit transcends merely cracking machines; it’s a testament to my dedication to learning and growth. I am determined to navigate the challenges presented by WebSploit Labs, aiming to independently solve them without recourse to walkthroughs. This commitment aligns with my broader goal of obtaining the OSCP certification, and I see each challenge as an opportunity to refine my skills and knowledge.
Conclusion: In this dynamic journey of ethical hacking with WebSploit, my enthusiasm is fueled by a thirst for knowledge and a commitment to continuous learning. This experience is not just about overcoming challenges; it’s about cultivating a mindset that values ethical practices, embraces ongoing education, and upholds the principles of responsible hacking. I invite you to join me on this expedition, where the pursuit of cybersecurity excellence is woven into the fabric of curiosity, dedication, and a relentless commitment to continuous improvement.
